Einer der schlimmsten Albträume vieler IT Sicherheitsverantwortlichen ist eingetreten: die zentralen Fileserver werden verschlüsselt… Die wichtigste Frage ist nun:
Welche nächsten Schritte sind die Richtigen, um die Infektion einzudämmen?
Und genau darauf gibt dieses Whitepaper eine Antwort. Statt zentrale Systeme, wie eben Fileserver oder Datenbanken herunterzufahren, wird gezeigt, wie mit schnell umsetzbaren Tipps und Tricks die verursachenden Benutzerkonten und Systeme identifiziert und anschließend deren Zugriff geblockt werden kann. Dadurch wird die Infektion eingedämmt, ohne dass es zu weiteren Ausfällen kommt. All dies lässt sich mit etwas Vorbereitung und Übung bei Bedarf in weniger als 5 Minuten mit kostenlosen Tools umsetzen!
Kämpfen Sie gerade mit den Folgen eines Cryptolockers? Wir von Bee IT Security helfen! Kontaktieren Sie uns sofort und wir unterstützen bei der Umsetzung der hier beschriebenen Maßnahmen.

Vorraussetzungen
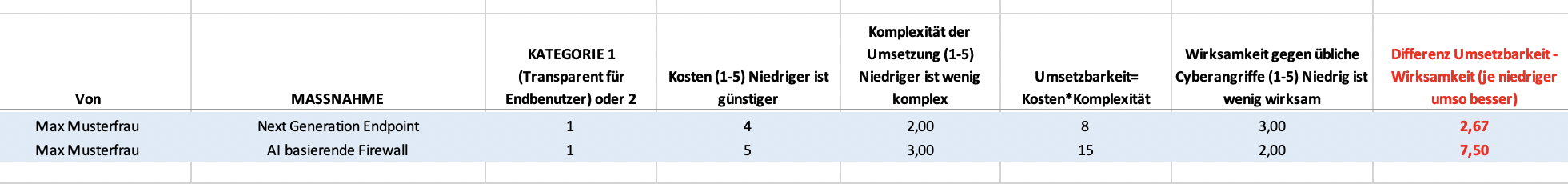
Damit die in diesem Whitepaper dokumentierte Herangehensweise umgesetzt werden kann, müssen einige Vorraussetzungen erfüllt sein:
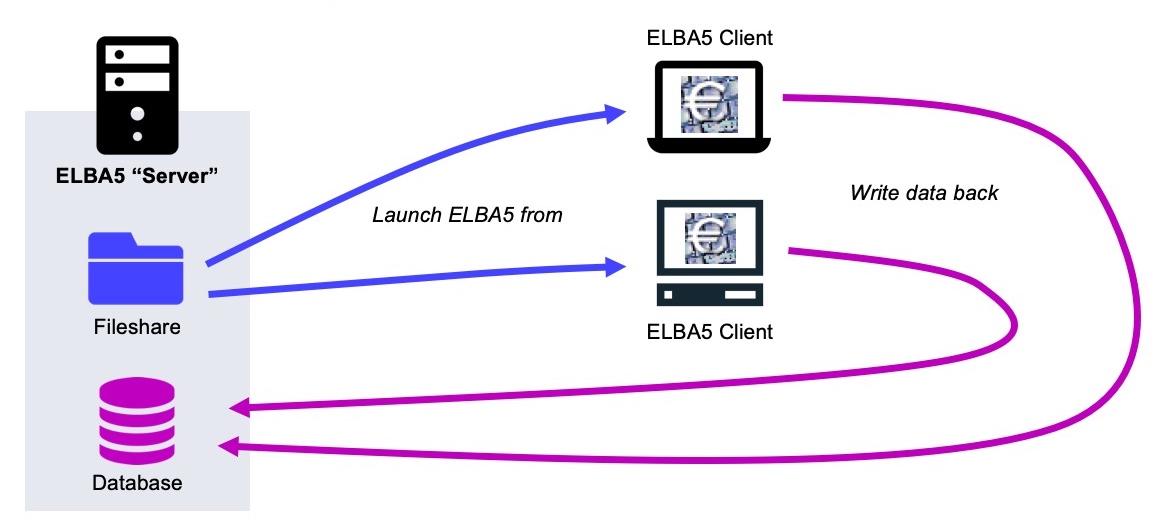
- Die Cryptolocker Infektion betrifft einen zentralen Fileserver, welcher über einen oder mehrere Windows Server bereitgestellt wird. Die Sharing Technologie (z.B.: klassisches SMB oder DFS) spielt hier nur eine untergeordnete Rolle.
- Die Schadsoftware nutzt eine immer gleiche Dateiendung bzw. schreibt eine Informationsdatei mit ähnlichem Namen.
- Es werden die Berechtigungen benötigt, um auf diesen Servern ein Programm herunterzuladen (bzw. darauf zu kopieren) und mit administrativen Rechten zu starten.
- Um die Infektion einzudämmen, wird Zugriff auf den zentralen Verzeichnissdienst (meistens Active Directory) benötigt. Dadurch ist es möglich die betroffenen Nutzerkonten sofort zu sperren.
- Im Idealfall: keine akute Cryptolocker Infektion, sondern Zeit für die Vorbereitung!
Ausgangspunkt
Ein falscher Klick kann ausreichen und der eigene Rechner ist mit Schadsoftware infiziert. Besonders Cryptolocker stellen hier seit bereits einigen Jahren eine akute Bedrohung dar. Immer wieder werden dabei von diesen „Erpressungs-Trojanern“ die klassischen Schutztechnologien, wie eben Virenscanner und Firewall, umgangen.
Einmal aktiv, beginnen Cryptolocker oft nun nicht mehr mit der Verschlüsselung des jeweiligen Endgerätes, sonders attackieren sofort die verbundenen Netzlaufwerke. Dieses Vorgehen macht sich für die Angreifer auch bezahlt: Der Ausfall eines Endnutzer-PCs kann meist ohne größere Beeinflussung des Betriebs verschmerzt werden. Sind jedoch die zentralen Dateiserver betroffen, können Teams, möglicherweise gar Abteilungen oder im schlimmsten Fall das ganze Unternehmen nicht mehr weiterarbeiten.
Kommt es in Unternehmen zu einem solchen Vorfall, werden oft – um vermeidlich Zeit zu gewinnen –die betroffenen Server herunterzufahren. Obwohl dies natürlich hilft den Schaden zu begrenzen, bringt es zwei gravierende Nachteile mit sich:
- Unabhängig vom eigentlichen Problem, ist es nun keinem Mitarbeiter mehr möglich auf Daten zuzugreifen. Soll heißen, obwohl der Schaden beispielsweise auf Grund der Dateisystemberechtigungen sehr beschränkt gewesen wäre, kann nun von niemanden mehr weitergearbeitet werden. Oft werden in diesem Zusammenhang auch automatisierte Prozesse – wie z.B.: der Stücklistenexport für die Produktion, der jeder Stunde durchgeführt werden muss – vergessen. Daher ist es, bevor kritische Systeme heruntergefahren werden, immer sehr wichtig den dadurch selbst verursachten Schaden zu bedenken!
- Windows Dateiserver schreiben in der Standardkonfiguration keine Audit Logs für Filesystem Operationen. Dies ist besonders problematisch da, sobald der betroffenen Server heruntergefahren wurde, der Verschlüsselungsvorgang am betroffenen Client abgebrochen wird. Dies macht jedoch die Lokalisierung der initialen Infektionsquelle sehr schwierig.
Rein über die Dateisystemberechtigungen kann versucht werden herauszufinden, welche Benutzer bzw. Endgeräte als „Patient Zero“ infrage kommen. Jedes dieser Systeme muss anschließend manuell auf Infektionszeichen geprüft werden. Besonders wenn von vielen Benutzer genutzte Freigaben betroffen sind, handelt es sich dabei um einen äußerst mühsamen und langwierigen Prozess. Es ist jedoch unerlässlich die initiale Infektion zu bereinigen, da diese an sonst jederzeit wieder ausbrechen kann.
Das Prinzip: „Cryptolocker eindämmen leicht gemacht“
Daher ist es entscheidend möglichst schnell diese Quelle zu erkennen. Genau darauf zielt das Prinzip „Cryptolocker eindämmen leicht gemacht“ ab. Um das weitere Vorgehen zu verstehen, ist wichtig sich zu überlegen, welche Operationen von Cryptolockern ausgeführt und welche davon leicht erkannt werden können:
Ordnerinhalte auflisten
Zu Beginn bzw. während der Verschlüsselung, werden die zu verschlüsselnden Dateien rekursiv aufgelistet. Dabei handelt es sich um einen sehr ressourcenintensiven Prozess (I/O und Netzwerk) der jedoch nicht ohne spezielle Tools bzw. Konfigurationen detektiert werden kann.
Verschlüsselung
Die Verschlüsselung an sich passiert auf dem infizierten Client. Die dazu aufgewendete CPU Performance kann zwar mit Monitoring theoretisch erkannt werden, praktisch ist dies jedoch – selbst wenn diese Tools überhaupt zur Verfügung stehen – nur sehr schwierig möglich.
Malware Infektion
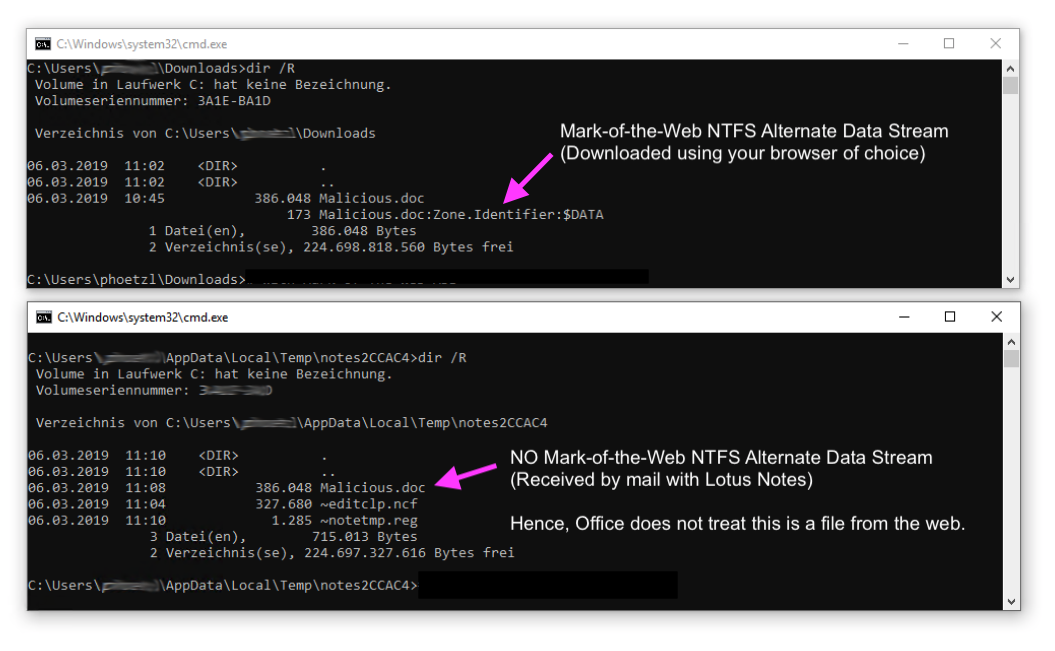
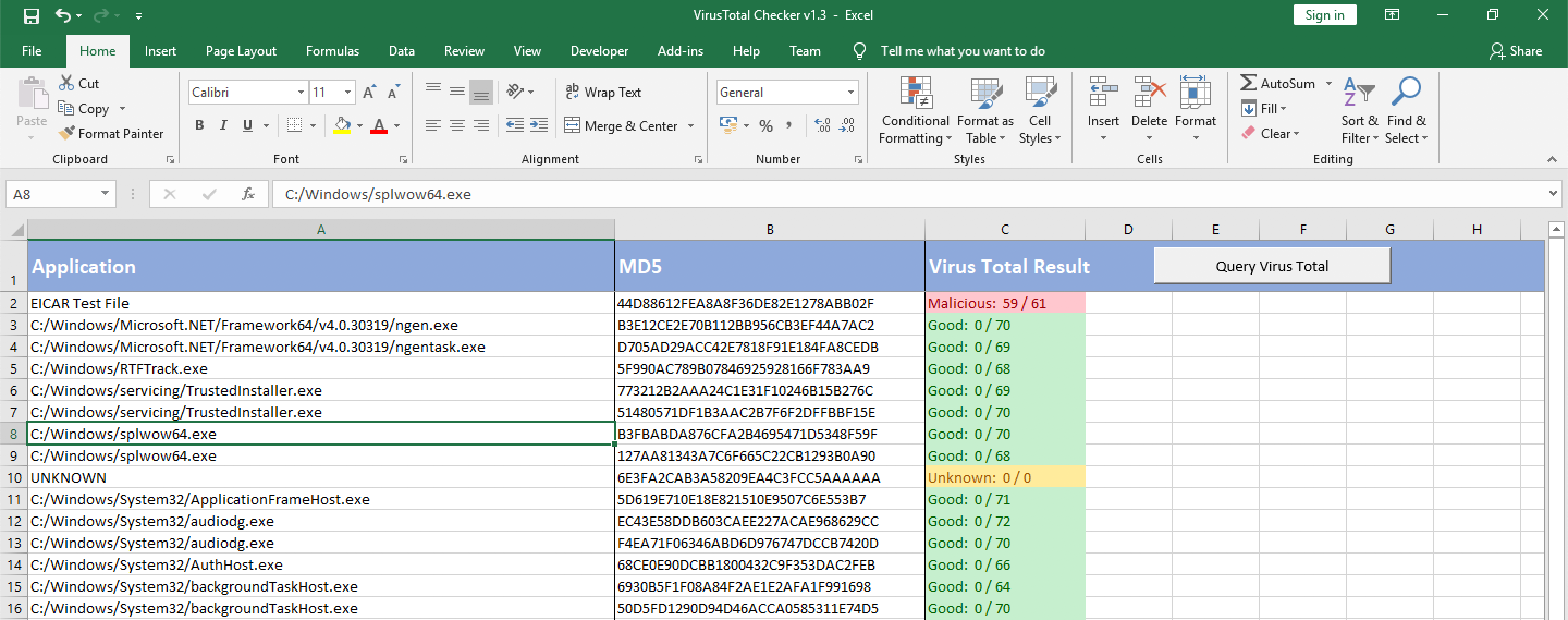
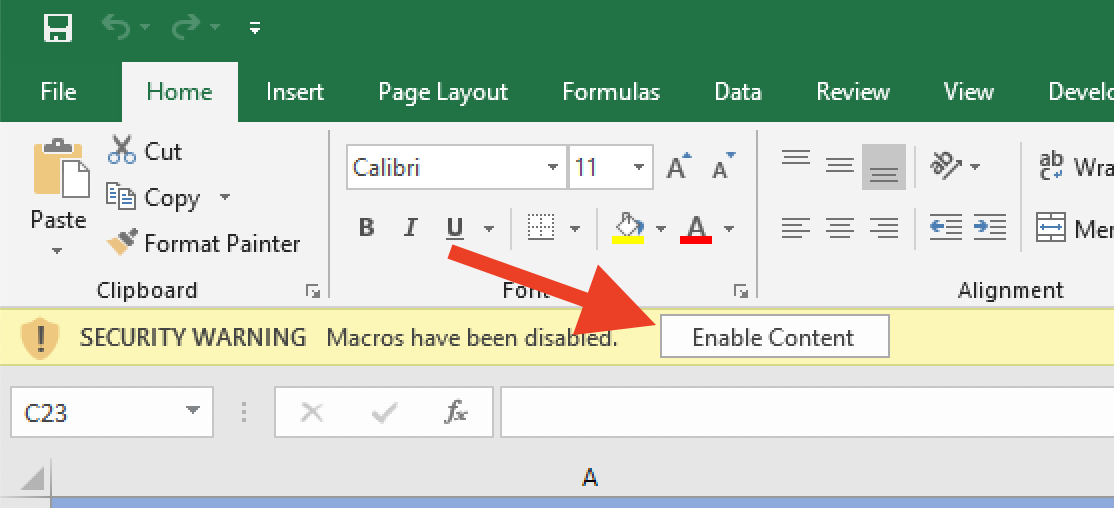
Die Schadsoftware an sich kann leider auch nicht einfach detektiert werden. Eine erfolgreiche Infektion war ja nur möglich, weil: 1.) kein Virenscanner am betroffenen Gerät installiert ist oder 2.) die Schadsoftware noch nicht von der eingesetzten Lösung erkannt wird.
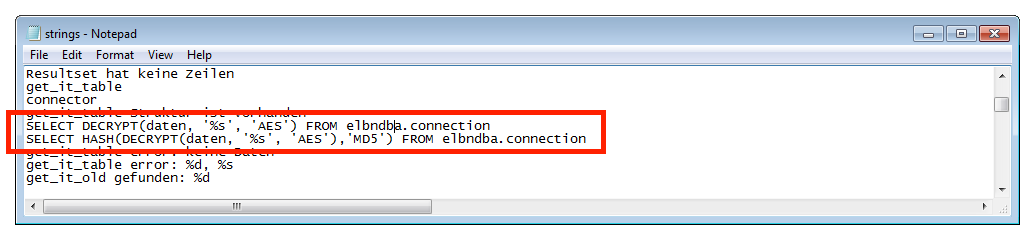
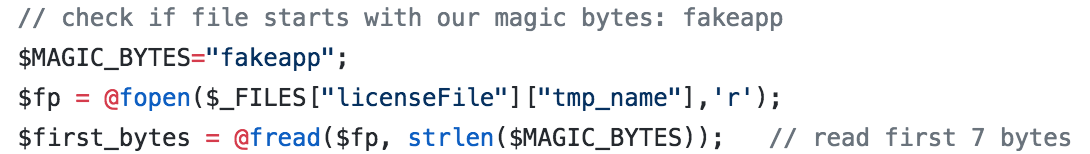
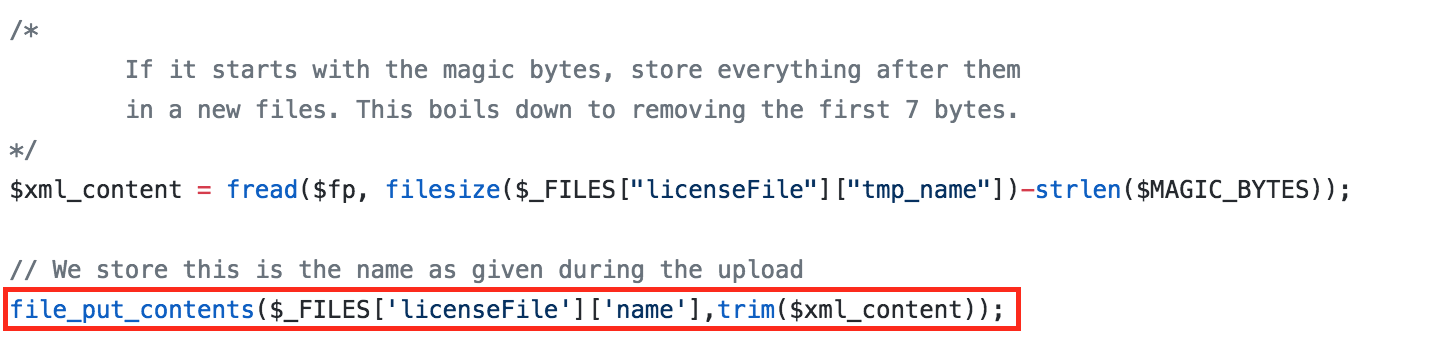
Schreiben der verschlüsselten Dateien bzw. der Informationsdatei
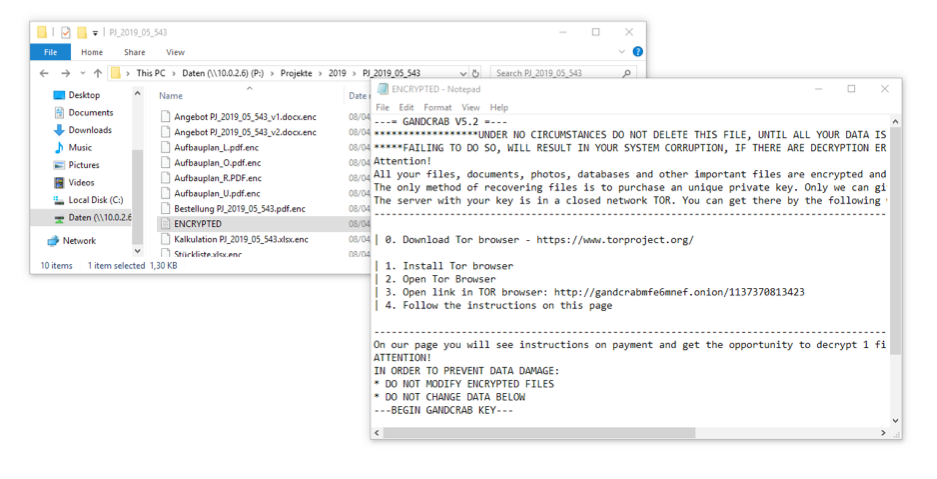
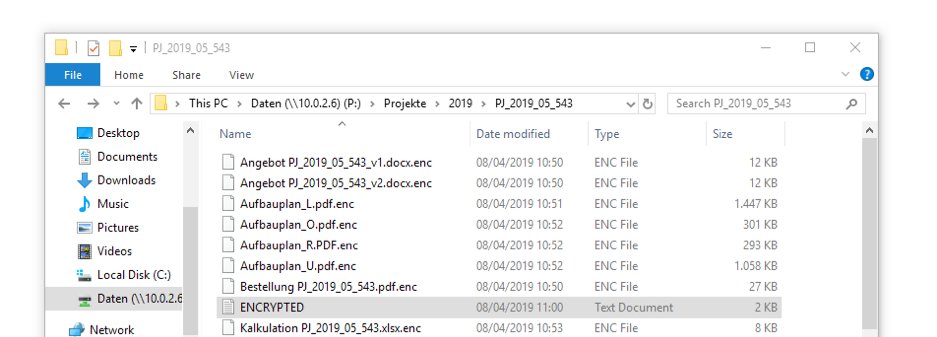
Nachdem der Cryptolocker die Dateien verschlüsselt hat, werden diese wieder in den Originalordner zurückgeschrieben. Damit der Cryptolocker erkennt, welche Dateien bereits verschlüsselt wurden, wird dabei meistens eine neue Endung an den Dateinamen angefügt (aus Vertrag.docx wird so z.B.: Vertrag.docx.enc). Damit der Nutzer versteht, was mit den Dateien passiert ist und außerdem zur Zahlung des Lösegelds aufgefordert werden kann, wird meistens zusätzlich eine Informationsdatei (z.B.: ENCRYPTED.txt) in allen betroffenen Ordnern erstellt.
Genau diese beiden Vorgänge eigenen sich hervorragend, um einen aktuell laufenden Cryptolocker zu erkennen.
Das Tool der Wahl: der Process Monitor
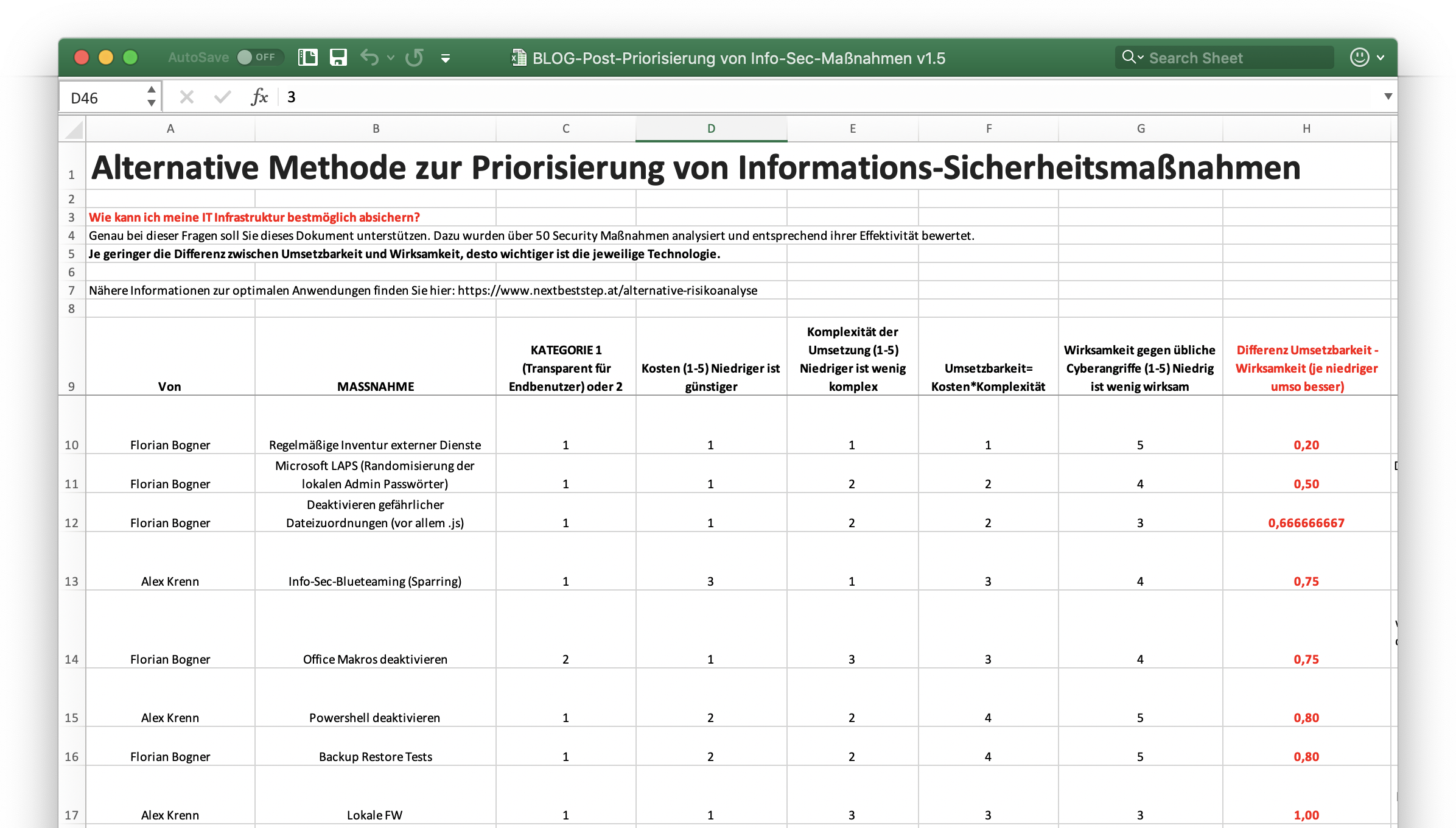
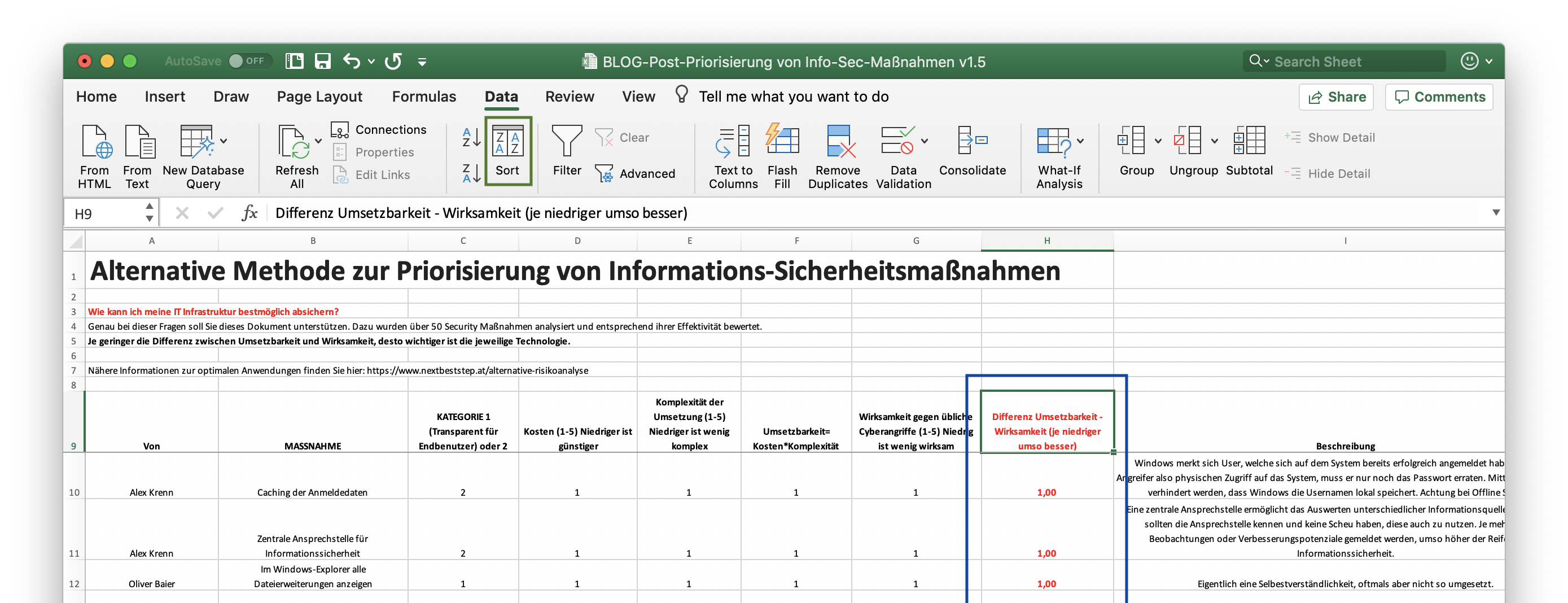
Nur wie können solche Aktivitäten sichtbar gemacht werden? Am einfachsten geht dies mit dem von Microsoft kostenlos zur Verfügung gestelltem Tool „Process Monitor“. Damit ist es möglich, die Windows Systemaktivitäten zu protokollieren und auszuwerten:
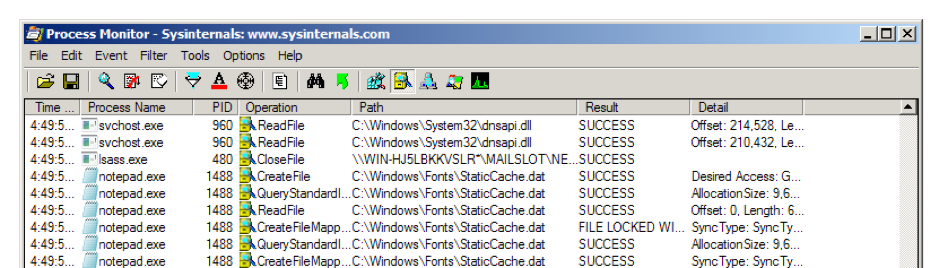
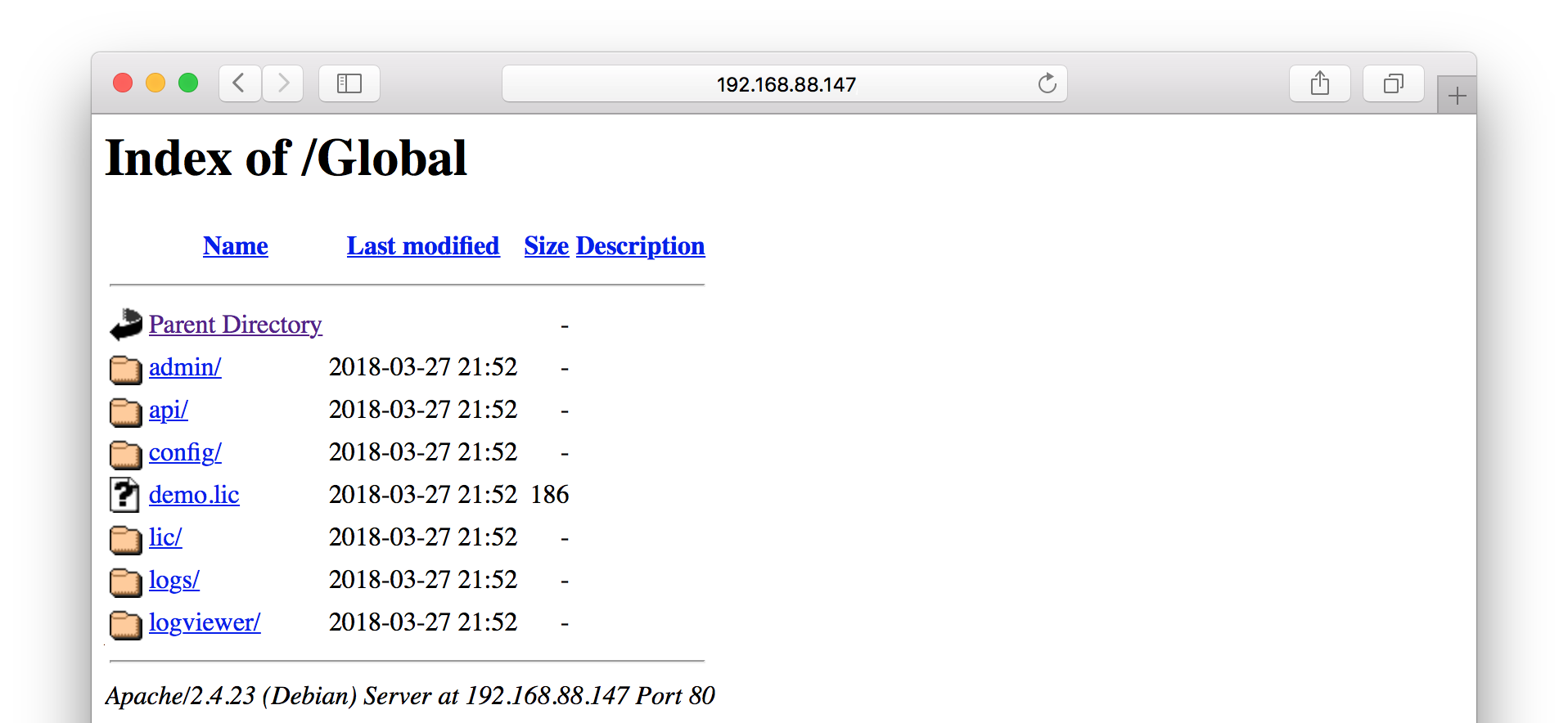
Daher muss dieses kleine Programm auf dem oder den betroffenen Servern heruntergeladen und als Administrator gestartet werden. Ab diesem Zeitpunkt werden alle Systemaktivitäten protokolliert. Besonders auf Fileservern, die von vielen Benutzern verwendet werden, können diese Informationen nicht ohne weitere Konfiguration ausgewertet werden.
Aktivitäten des Dateiservers aufzeichnen
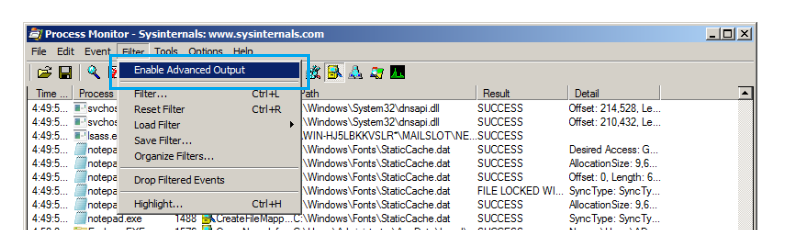
Besonders wichtig bei der Nutzung des Process Monitors für die Erkennung von Vorgängen auf Dateifreigaben ist die Aktivierung des „Advanced Output“. Erst damit werden Aktivitäten auf Freigaben (z.B.: SMB, DFS) überhaupt sichtbar. Standardmäßig werden diese Daten nicht protokolliert bzw. angezeigt.
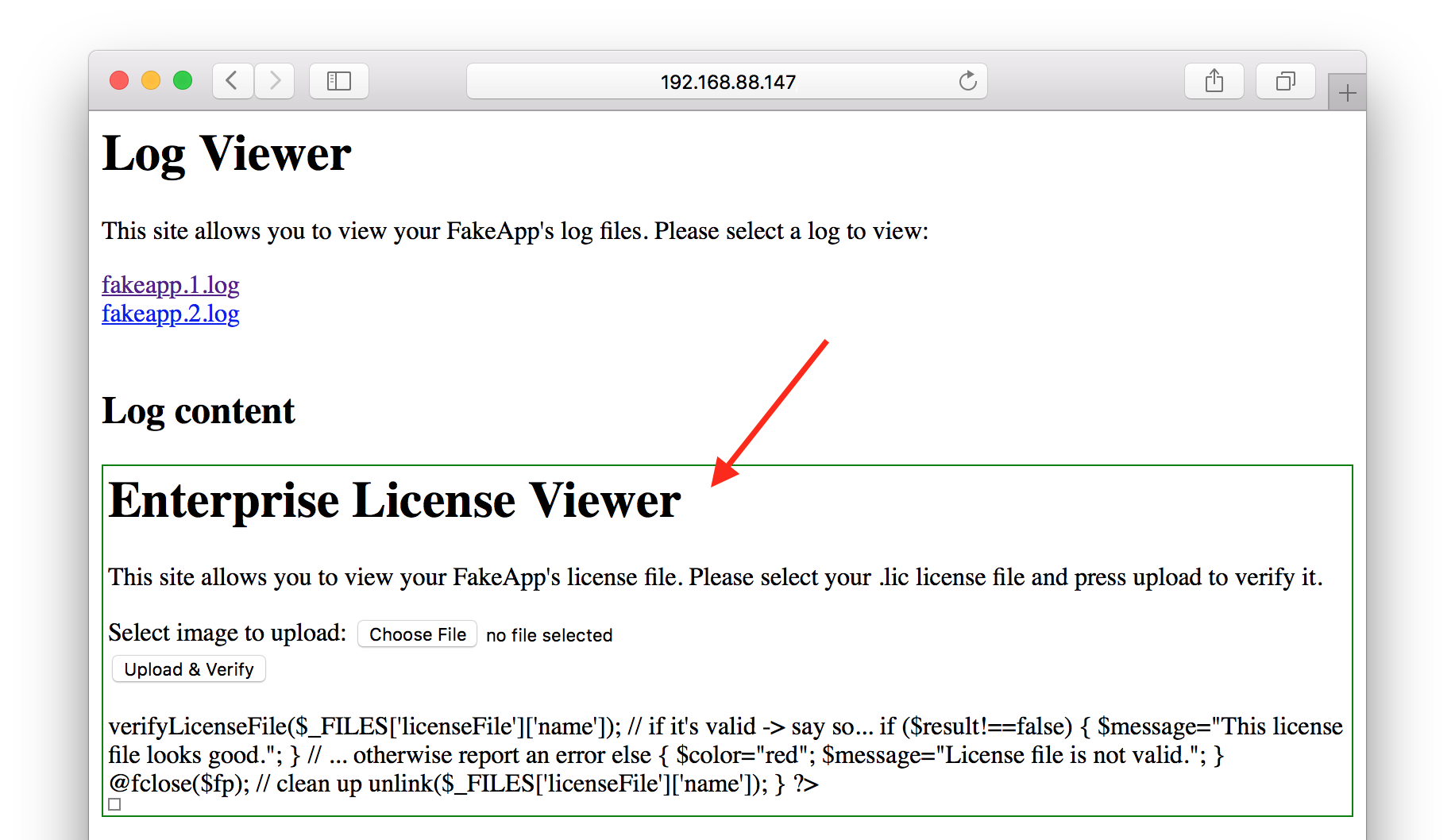
Filter setzen
Im nächsten Schritt müssen über die „Filter“ Funktion die Informationen eingeschränkt werden. Zu Beginn empfiehlt es sich hier über die Symbolleiste nur mehr Dateisystemoperationen zu betrachten (1). Anschließend kann über den Dialog „Process Monitor Filter“ (Menü Filter -> Filter…) genau definiert werden, welche Operationen geloggt werden sollen (2):
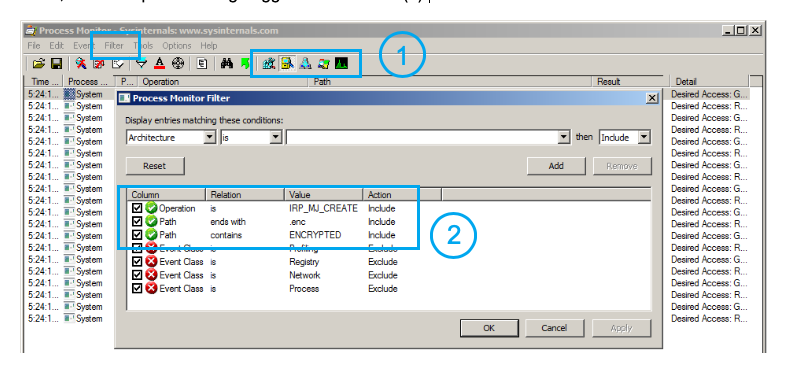
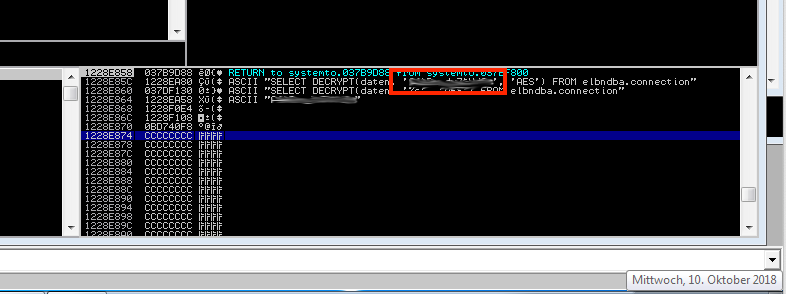
Hier ist es entscheidend die Konfiguration für den jeweiligen Cryptolocker anzupassen. Lediglich die erste Zeile („Operation is IRP_MJ_CREATE: Include“) kann immer direkt übernommen werden. Damit werden nur mehr Operationen für die Erstellung von neuen Dateien und Verzeichnissen betrachtet.
Werden vom Cryptolocker die verschlüsselten Dateien mit der Dateiendung .enc abgelegt, kann beispielsweise der folgende Filter verwendet werden: „Path ends with .enc: Include“. Dadurch werden nur mehr Dateien betrachtet, deren Name mit .enc endet.
Enthält die Informationsdatei beispielsweise immer ENCRYPTED im Dateinamen hilft der Filter „Path contains ENCRYPTED: Include“
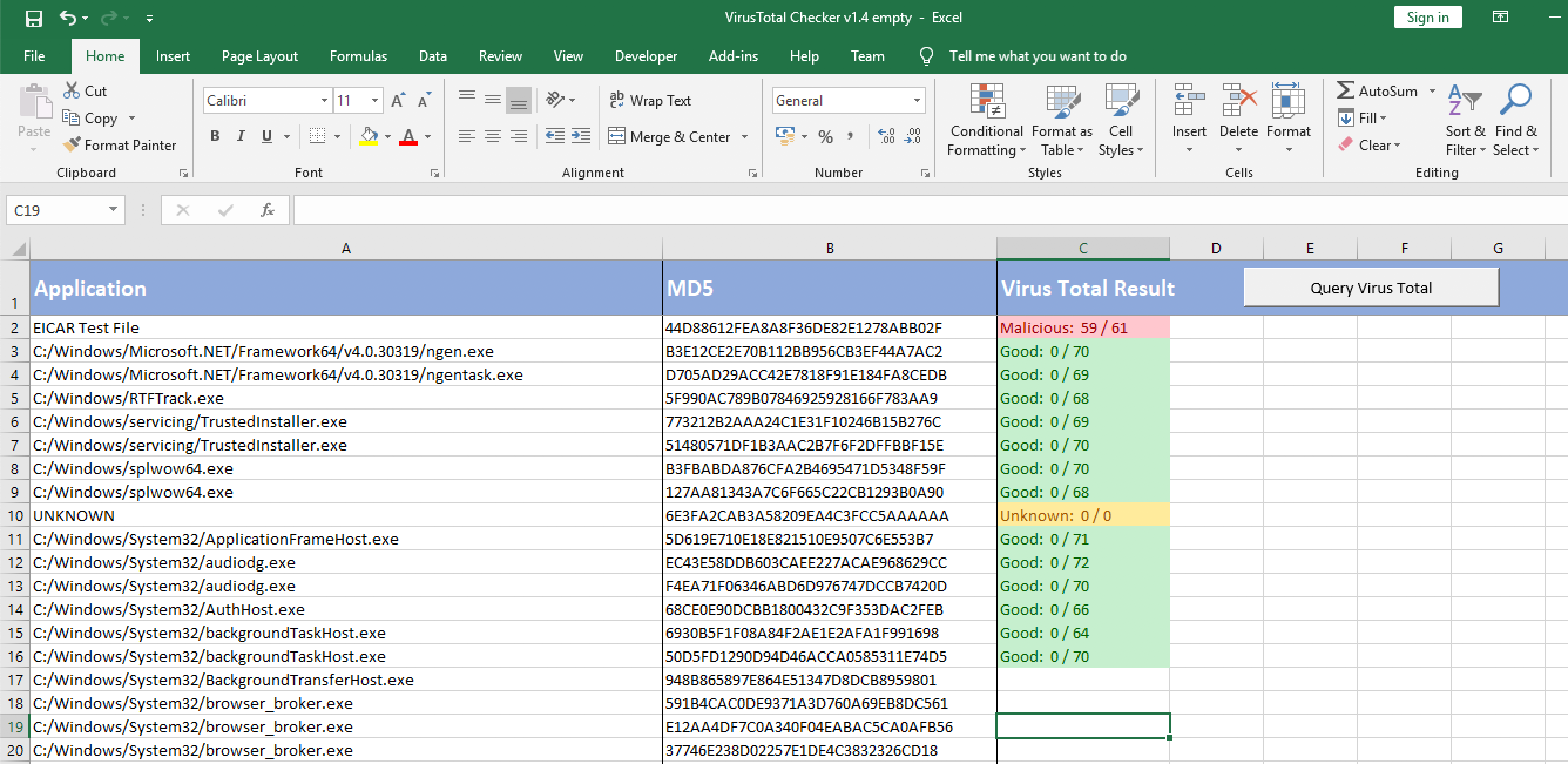
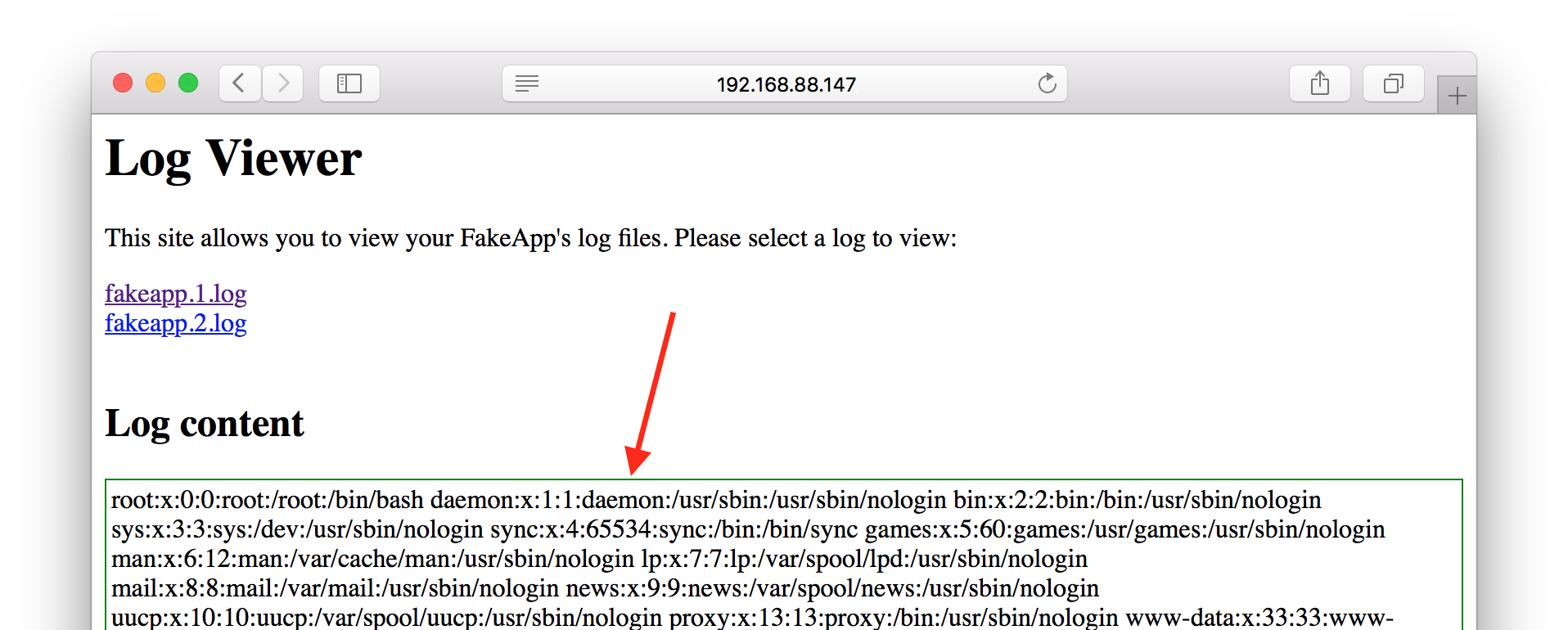
Auswerten der Loginformationen
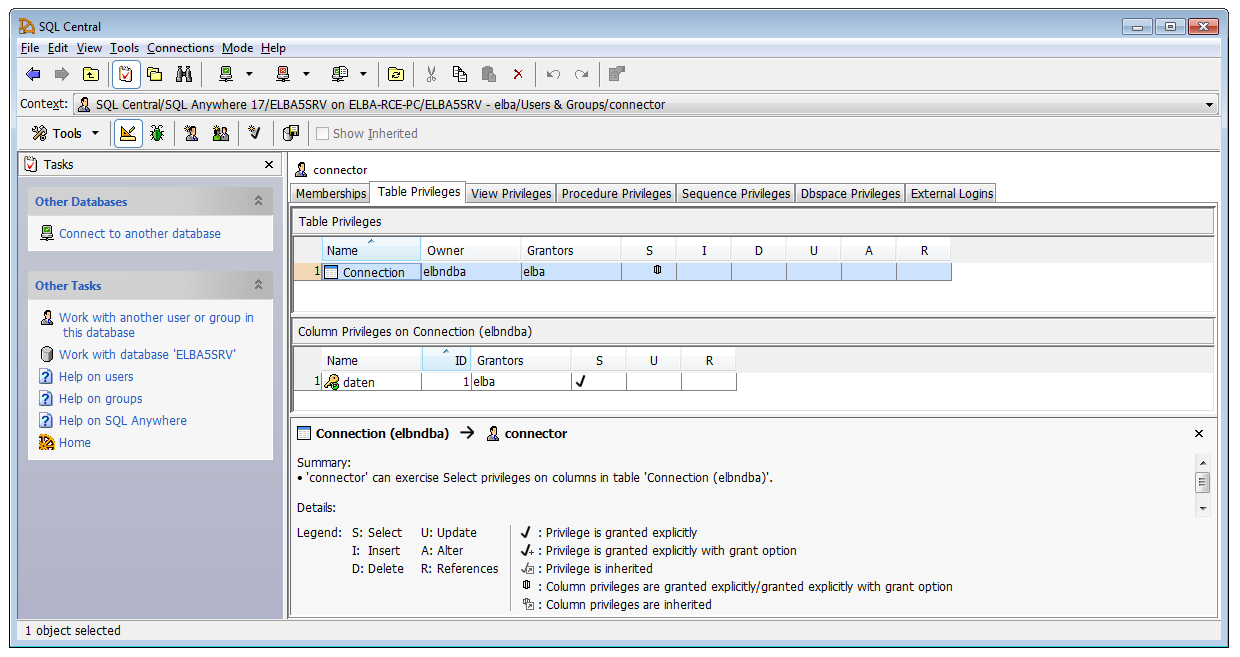
Sobald diese Filterkonfiguration angewendet wurde, werden nur mehr die vom Cryptolocker verursachten Dateisystem Operationen angezeigt. Platziert man anschließend den Mauszeiger über einen Eintrag der Spalte „Detail“, wird der jeweilige Benutzername angezeigt, der diesen Schreibvorgang initiierte.
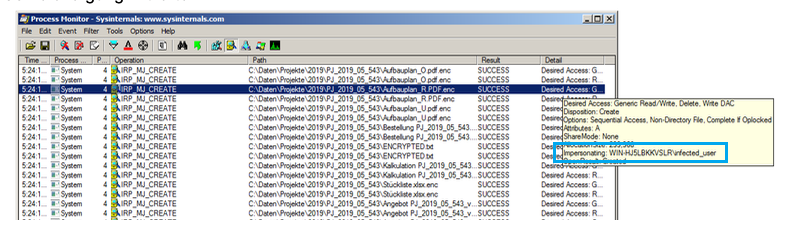
Dabei handelt es sich um das Benutzerkonto des Anwenders, der als „Patient Zero“ für die Verschlüsselung verantwortlich ist.
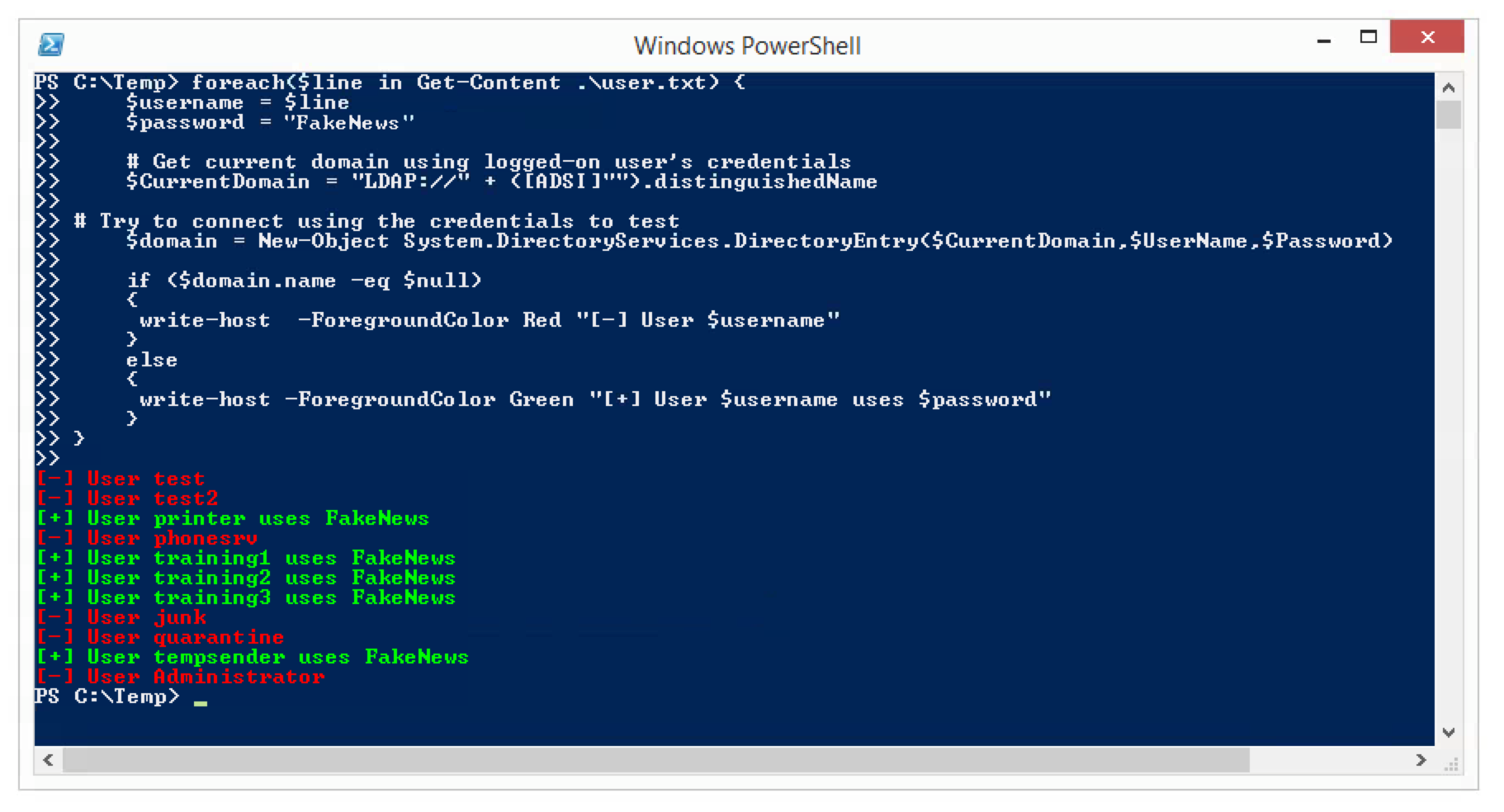
Stoppen der Infektion
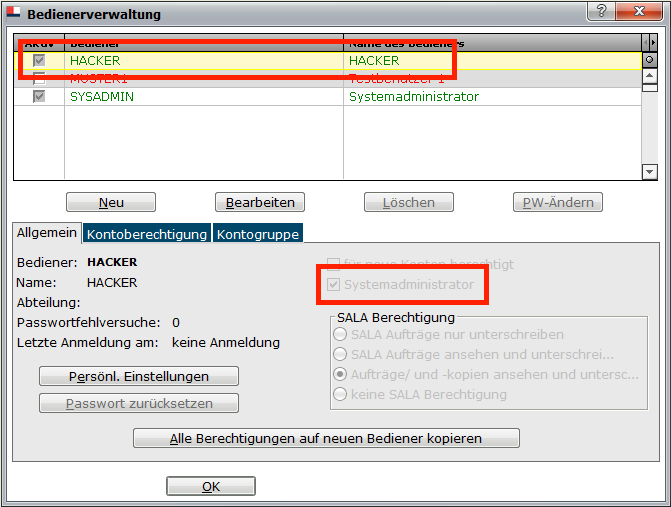
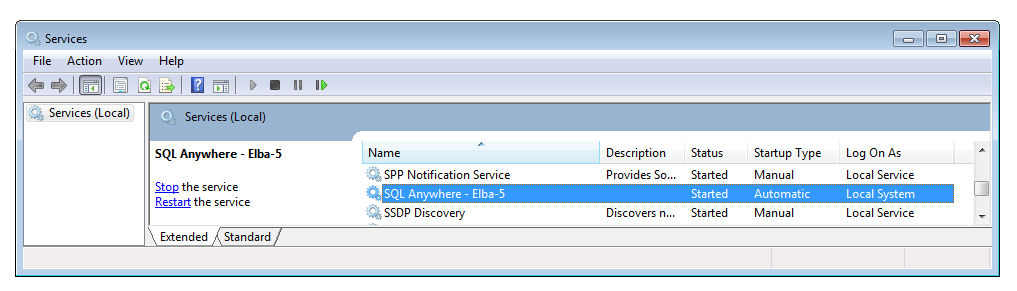
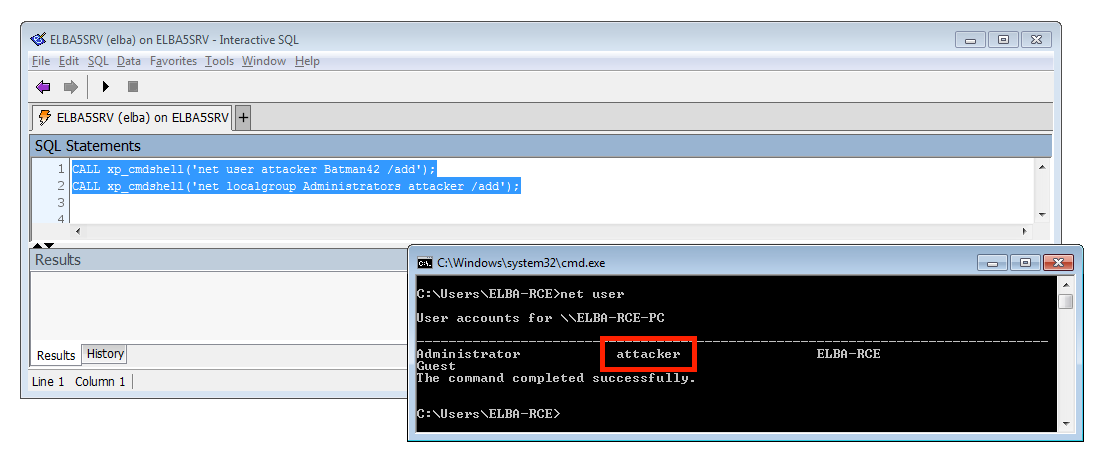
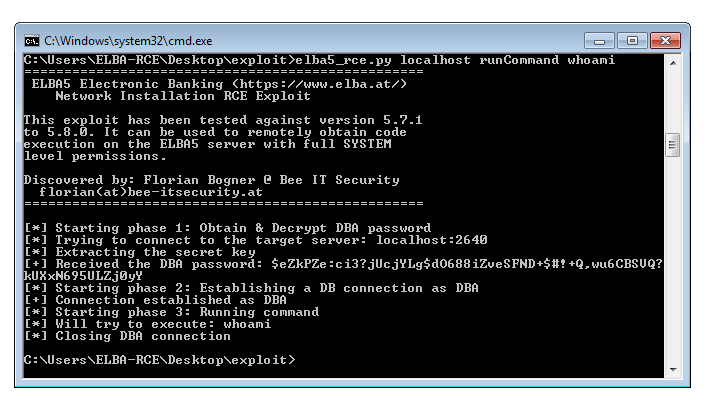
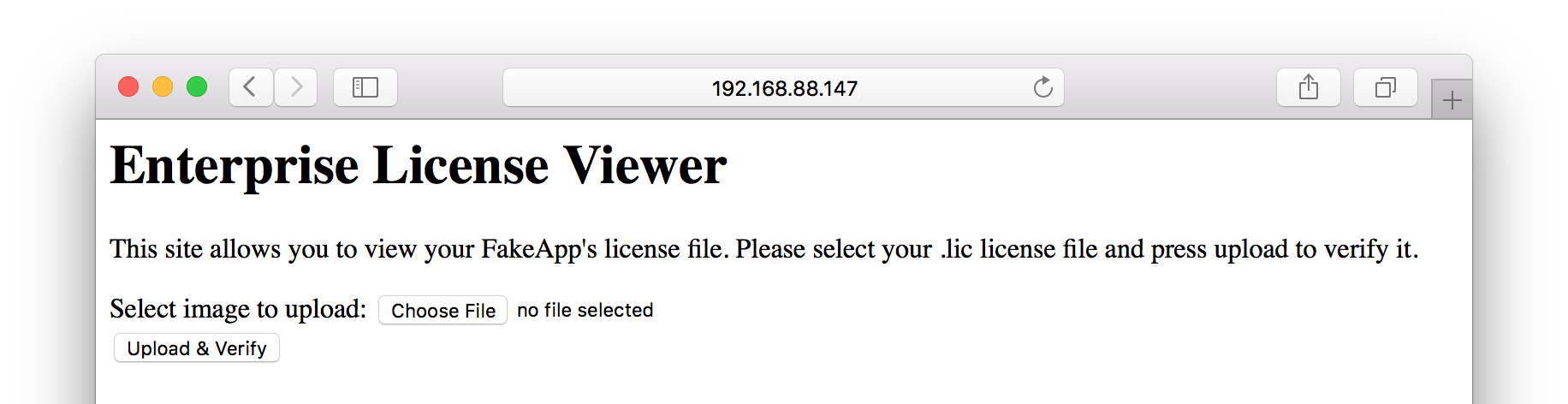
Ausgestattet mit diesem Wissen kann nun gehandelt werden. Es empfiehlt sich sofort das betroffene Benutzerkonto zu deaktivieren:

Über das Computer Management sollten außerdem alle bestehenden Sessions sofort beendet werden:
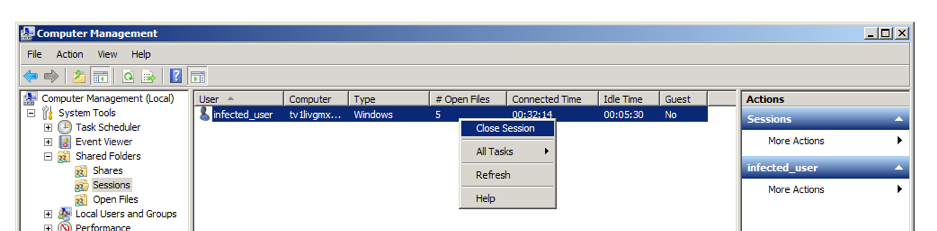
Das betroffene Gerät sollte nun natürlich auch vom Netzwerk getrennt werden.
Fazit
Durch das in diesem Whitepaper dokumentierte Vorgehen ist es möglich eine akute Cryptolocker Infektion in nur wenigen Minuten zu lokalisieren und entsprechende Gegenmaßnahmen einzuleiten.
Damit ist es nicht notwendig zentrale Systeme herunterzufahren, sondern nur gezielt die wirklich betroffenen Benutzerkonten zu sperren. Dies vermeidet unnötige Ausfälle und hilft so die Incident Behebung erheblich zu beschleunigen. Das beschriebene Verfahren wurde durch Experten der Bee IT Security schon vielfach eingesetzt und wird daher vollumfänglich empfohlen!
Wichtig ist, dass nachdem die Infektion eingedämmt werden konnte, eine weitere Analyse gestartet werden muss. Dabei ist zu beantworten, wie der Cryptolocker überhaupt die bestehenden Schutzmechanismen umgehen konnte und wie entsprechende Angriffe in Zukunft verhindert werden können.