Recently some colleagues and I discussed the possibility to obfuscate known malware samples so that they successfully pass a virus scan. This works because most scanning engines detect threats due to their signature. These signatures in turn are based on the program code of the malware. An attacker can now modify or obfuscate the source code of already known malware and thereby avoids detection.
As we were unsure about the real-world feasability and the ease of use of the available obfuscation tools I decided to test one of them: The Veil-Framework. To do so I set up a fully patched Windows 7 Professional 32Bit VM secured with AVG AntiVirus FREE 2015 with the goal to modify a previously detected and blocked malware so that it sucessfully executes.
Creating the malware
The first thing I had to do was to create a malware for this test. As I wanted a “safe” malware, I decided to use the Metasploit windows/messagebox payload. It only opens a messagebox but it is detected as malicious by many scanners.
To ensure that we use exactly the same source for all further tests I used the msfpayload command line utility to create a Windows application (malware.exe) and to dump the corresponding raw shellcode (malware.raw)
msfpayload windows/messagebox TITLE="Malware" TEXT="Malware executed" ICON="WARNING" X >malware.exe msfpayload windows/messagebox TITLE="Malware" TEXT="Malware executed" ICON="WARNING" R >malware.raw
As expected, the unobfuscated malware (malware.exe) was immediately detected by the AVG scanning engine:
 So let’s move on to modify our malware by …
So let’s move on to modify our malware by …
Obfuscating the Shellcode
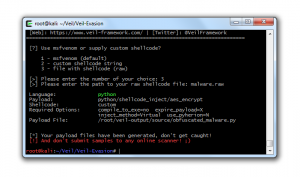
To do so we use Veil-Evasion that is part of the Veil-Framework. The following command creates an obfuscated python script that contains the original AES encrypted shellcode with the help of the python/shellcode_inject/aes_encrypt payload.
./Veil-Evasion.py -p python/shellcode_inject/aes_encrypt -c compile_to_exe=no --overwrite -o obfuscated_malware
Before the obfuscation progress starts we have to provide the previously created raw shellcode of our malware:
Veil-Evasion supports many different programming languages (C, CS, Powershell, Python, …) and methods (shellcode injection, different meterpreter payloads, …) for obfuscation. For an up-to-date list browse the payloads subfolder in the source code repository.
Although the Veil-Framework is capable of directly creating a Windows application I had some problems with the thereto necessary Wine installation. As a workaround I simply copied the obfuscated malware to my Windows computer and used PyInstaller to convert it there to a self contained application.
C:\Temp>C:\Python27\Scripts\pyinstaller.exe --onefile obfuscated_malware.py
In the background PyInstaller analyses the Python script and packs all the necessary modules and libraries including the Python Runtime into a single and redistributable Windows application.
Playing Hide & Seek
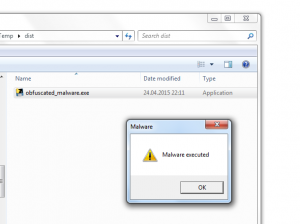
Finally I copied the newly obfuscated malware to the test machine and double clicked it. To my pleasure, it passed the on-access virus scan and executed.
As I was eager to know how well I masked my “malicious” intends I uploaded the file to VirusTotal. Although it was detected by 7 out of 56 scanners this is still a major improvement over the initial 35 detections.
Conclusion
With this demo I clearly showed that it is fairly easy for malware applications to avoid detection from off-the-shelf virus scanners by using obfuscation. This targeted attacks are hard to mitigate and they require special security tools with for example virtualisation and malware analysis capabilities to do so. The good thing is that modified malware will most likely be detected by virus scanners within days after their initial deployments. Additionally more and more engines already detect the obfuscation itself and also block the file.
This all boils down to the fact that virus scanners are only one tool in the ongoing fight for protecting your critical infrastructure.